The introduction of autonomous AI agents into everyday production environments has brought forth significant advancements, but it has also exposed a growing security challenge. As these AI entities begin to operate similarly to humans, they require the same access privileges. To address this emerging issue, 1Password has launched Unified Access, a platform aimed at tracking agent activities, centralizing their credentials, and enforcing security policies at scale.
The concept is simple: rather than retaining long-lived API keys in scripts or configuration files, agents should retrieve secrets on demand from an encrypted vault. This process is tightly controlled, ensuring that every access is linked back to a specific human or machine identity. This strategy mirrors established practices for human users, now refined for the era of AI agents.
Why AI Agents Challenge Traditional Identity Models
AI agents operate differently from conventional service accounts. They seamlessly integrate various tools, access internal APIs, initiate workflows, and often work alongside other agents. This fluidity prompts teams to hard-code credentials into notebooks, store secrets in environment variables, or copy tokens into chat prompts, inadvertently exposing sensitive information.
Security experts have consistently highlighted this risk. The OWASP Top 10 for LLM Applications cautions against prompt injection and the leakage of secrets. Research from MIT has also shown how agents can unexpectedly link tools in unanticipated ways, complicating security measures. IBM’s Cost of a Data Breach report reveals that stolen or compromised credentials account for 19% of detected breaches, underscoring that the proliferation of secrets is a broad systemic concern.
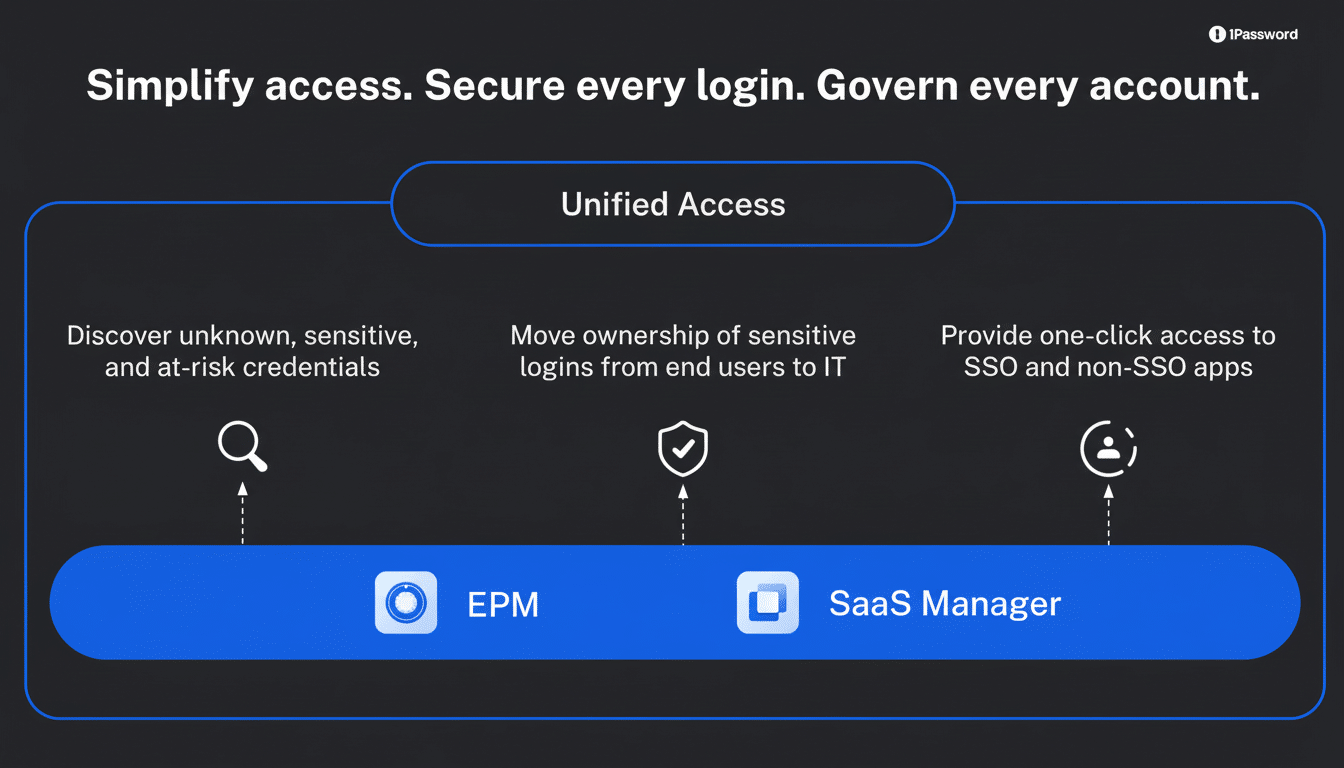
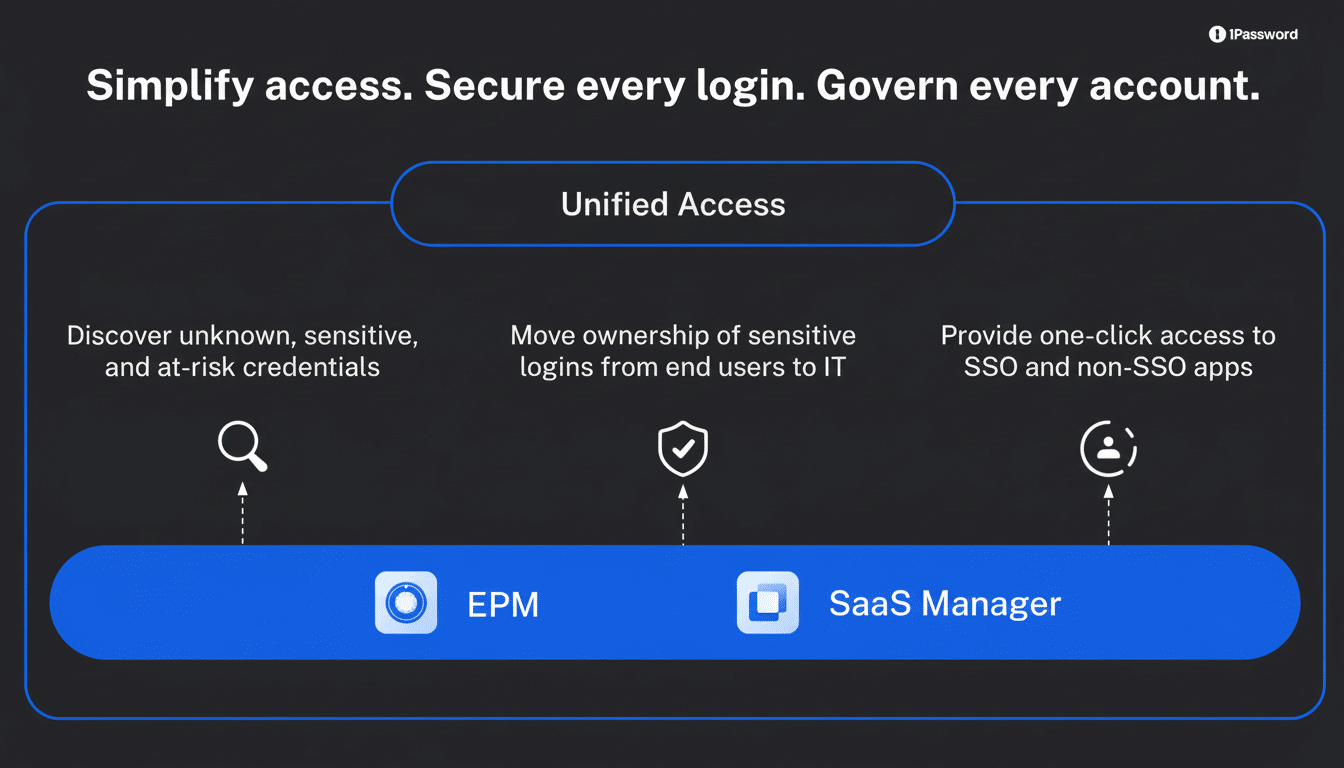
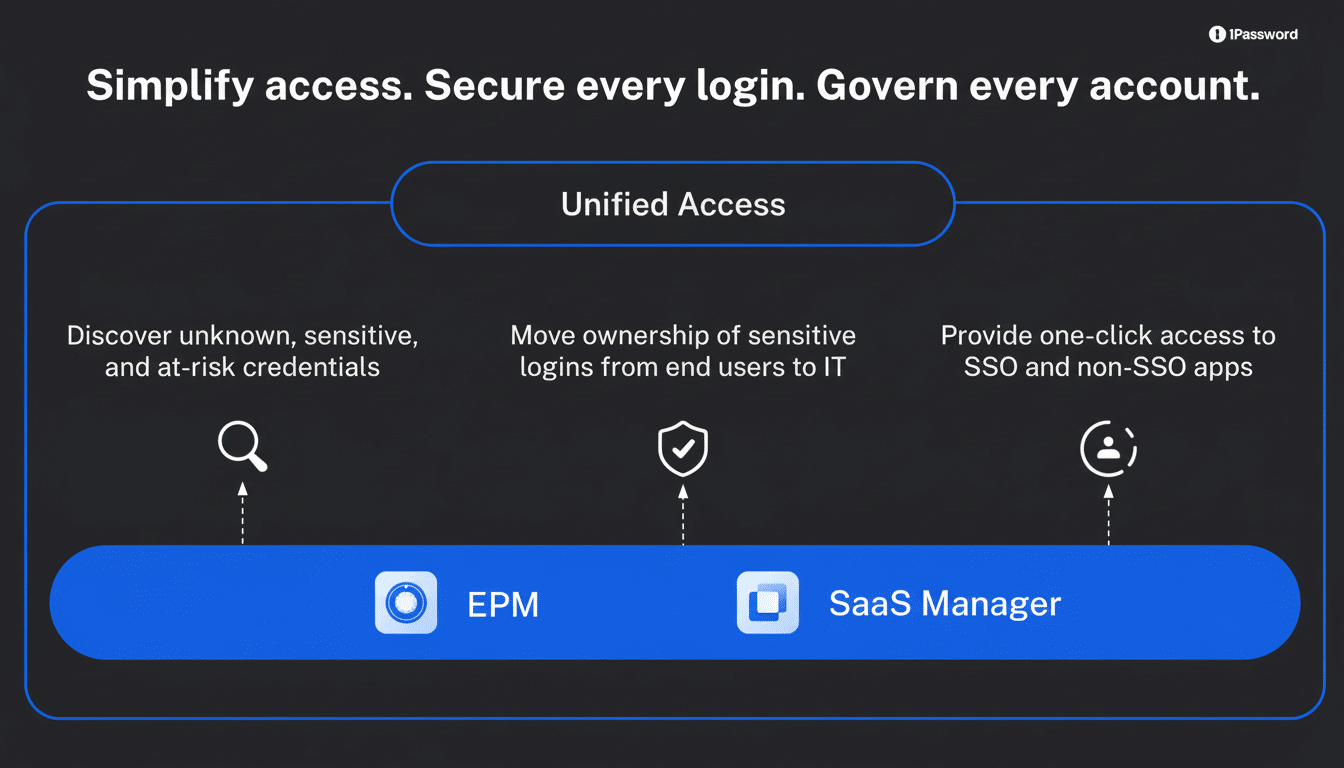
Inside Unified Access: Managing Agent Secrets
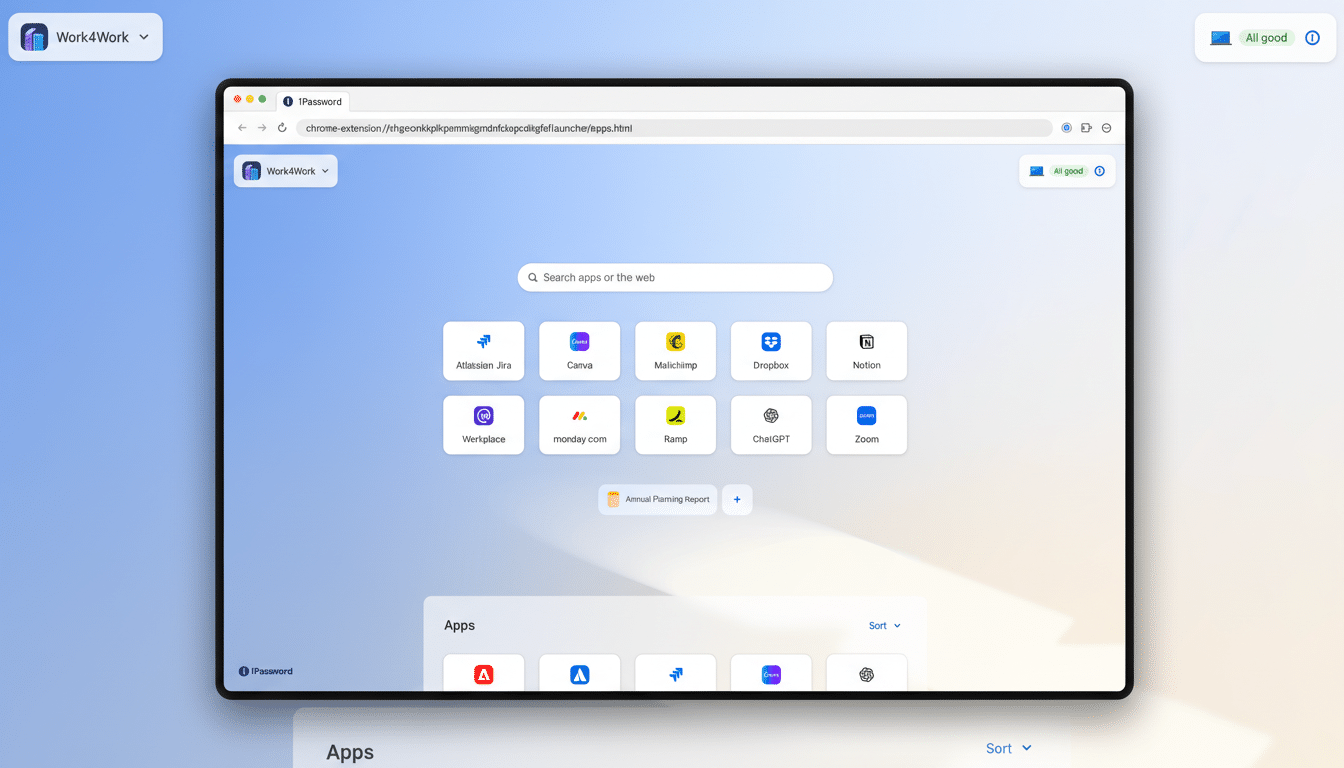
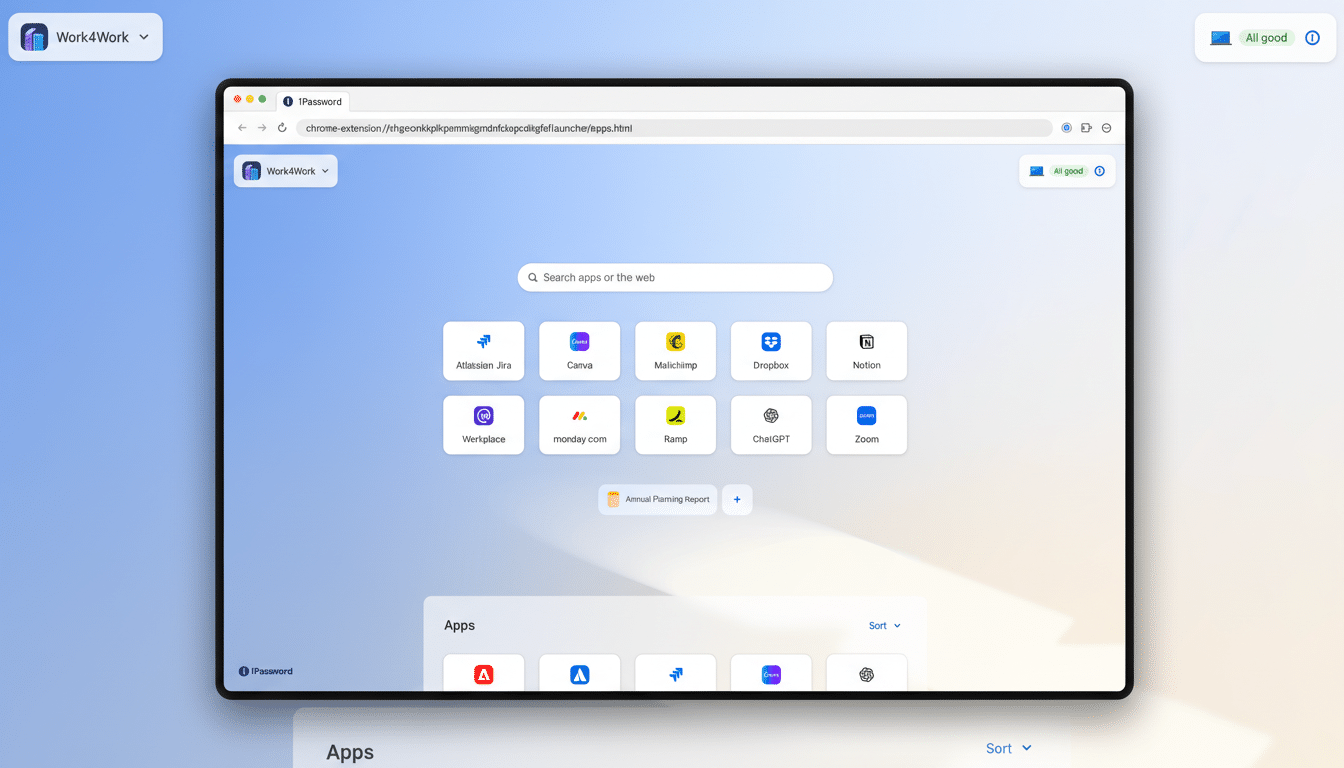
1Password’s strategy revolves around three core actions: discovery, security, and auditing. Initially, the platform scans for agent activities and identifies exposed credentials across various endpoints, browsers, and local developer environments. This process uncovers plaintext files containing sensitive data, unencrypted SSH keys, and other security threats, enabling teams to recognize ‘shadow AI’ use they were unaware of.
Next, it centralizes all credentials within an encrypted vault and substitutes hard-coded keys with secure references. When an agent requests access at runtime, the platform enforces stringent policies regarding scope and expiration, ensuring that only authorized processes receive the secrets. This mechanism facilitates instant revocation and rotation of credentials without altering code, effectively addressing the lingering habit of keeping API keys indefinitely.
Lastly, it meticulously logs each access instance, specifying who accessed what, where, and when. These logs create a detailed audit trail that supports compliance and incident response teams. While the company promises further enhancements to its auditing capabilities, the functionalities for discovery and secure delivery are currently available.
Early Integrations Indicate Developer-Centric Design
To seamlessly integrate into existing workflows, 1Password has developed collaborations with development tools and platforms such as Cursor and GitHub, in addition to partnerships with cloud-native providers like Vercel. The goal is to incorporate security directly into integrated development environments (IDEs), sandboxes, and CI/CD pipelines, allowing engineers to work without the distraction of switching contexts or building custom integration solutions.
The company is also working with vendors associated with agent control systems, AI infrastructure, and Model Context Protocol gateways—creating the frameworks necessary for agents to discover tools and request access efficiently. As these integrations evolve, managing secrets will become an inherent aspect of agent operations rather than an afterthought.
Comparing with Major Identity Platform Providers
Unified Access enters a competitive landscape where large vendors are also confronting these identity challenges. Microsoft has recently showcased an identity layer tailored for agents within its system. In contrast, 1Password positions itself as vendor-agnostic, emphasizing the security of credentials and machine identities within diverse environments, rather than confining teams to a singular cloud or productivity suite.
This distinction is particularly relevant for organizations that are already using multiple clouds, data centers, and toolchains. In practice, many may find themselves adopting overlapping solutions—a cloud-based IAM system for broad access alongside a secrets management platform for precise, just-in-time access and auditing.
Security Tradeoffs and Governance Considerations
Centralizing secrets does raise essential trust issues. Systems tasked with extensive discovery and distribution capabilities become crucial components of security infrastructure and, consequently, prime targets for threats. 1Password’s approach focuses on minimizing persistent privileges, confining access to designated processes, and logging every access request. Enterprises must remain vigilant regarding key management practices, encryption strategies, and potential vulnerabilities, aligning their policies with established frameworks such as NIST’s AI Risk Management Framework and CISA’s Secure by Design guidance.
The governance advantages are considerable, including expedited credential rotation, reduced dependence on long-lived API keys, and increased accountability for agent activities. As machine identities proliferate and begin to outnumber human ones, the operational benefits of having a single source of truth can outweigh potential drawbacks, provided they are coupled with principles of least privilege, network segmentation, and ongoing monitoring.
Steps Security Leaders Should Take Now To Mitigate Risk
- Assess the agents and tools currently interacting with production environments. Shadow usage can grow unnoticed in pilot initiatives and makeshift scripts.
- Differentiate between human and agent credentials. Provide agents with narrowly scoped, expiring access tokens that are tied to specific roles and systems.
- Eliminate secrets from code, prompts, and environment variables. Use references that are resolved at runtime under established policies.
- Enable default rotation and revocation features. In case of behavioral changes in an agent or token leaks, there should be a quick termination method and an expedited process for new credentials.
- Maintain comprehensive logs and review them regularly. Ensuring accountability and traceability is crucial, especially when bots act on behalf of users or infrastructure.
AI agents have moved beyond being mere curiosities; they have become capable and, importantly, privileged entities in production. With the advent of Unified Access, 1Password is betting on the notion that the only sustainable method for scaling agent usage securely is to treat them as first-class identities, provide them with on-demand secrets, and maintain a thorough audit trail at every stage.